It has been a long time since I build a Microsoft Active Directory lab environment. Years ago, I put together a test lab with physical white box machines that I built. The popularity of virtual machine technology makes all of that space hogging, wires everywhere, make your wife annoyed mess a thing of the past.
This will be the first in a series of posts about how I setup a virtual test lab using VMware Fusion on my Mac.
Microsoft Insider Programs
I have been dabbling with virtual Ubuntu machines over the last year or so, and I wanted to do something a little different. Microsoft offers IT pros a few of their products free of charge, for non-production use, of course, for training and development purposes as part of the Insider program. IT types who want to play along will be interested in the Windows 10, Windows Server (Core), Visual Studio Preview, and SQL Server Developer. There are also programs for Microsoft Edge and Office 365, if you are so inclined.
Make Up of the Lab
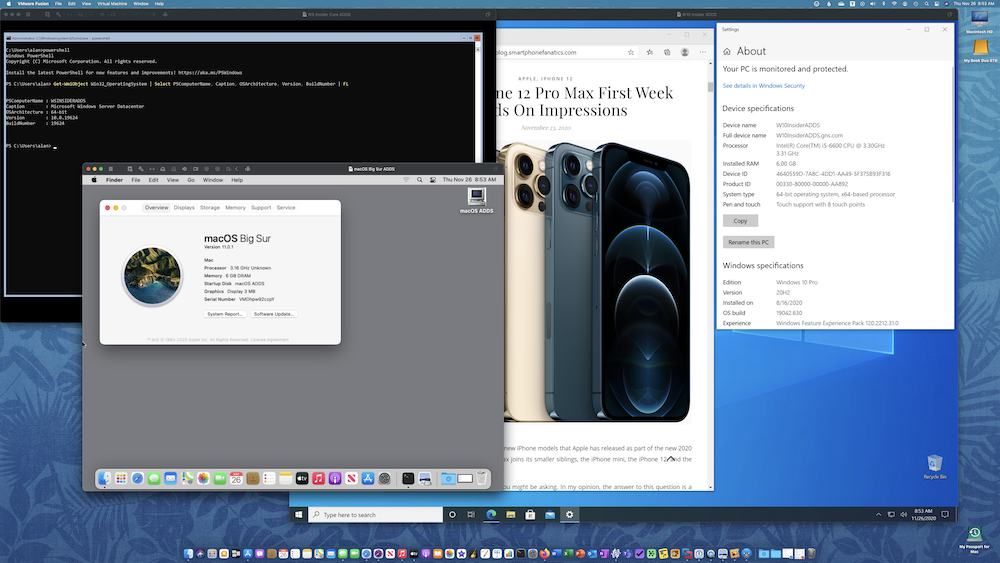
I’m looking for a playground so my requirements are pretty low. To build my virtual lab environment I will be using my everyday use 2015 5K iMac with a 3.3Ghz Quad-Core Intel Core i5 CPU and 32GB of RAM. Faster CPUs and more RAM is always better, however, in 2015 my needs were different. I am also running VMware Fusion Pro 12 as the hypervisor on my iMac. Due to the physical constrains of my iMac, not all of these virtual machines will be running all the time. Likewise, they will not be optimized for speed.
As a side note, anyone purchasing a new M1 Apple Silicon powered Macintosh – the 2020 MacBook Air, the 2020 2-port USB-C 13-inch MacBook Pro, or the 2020 silver Mac mini – will not currently be able to run virtualization technology like VMware Fusion or Parallels Desktop because these apps haven’t yet been updated to work on M1 and Apple’s new virtualization technology layer.
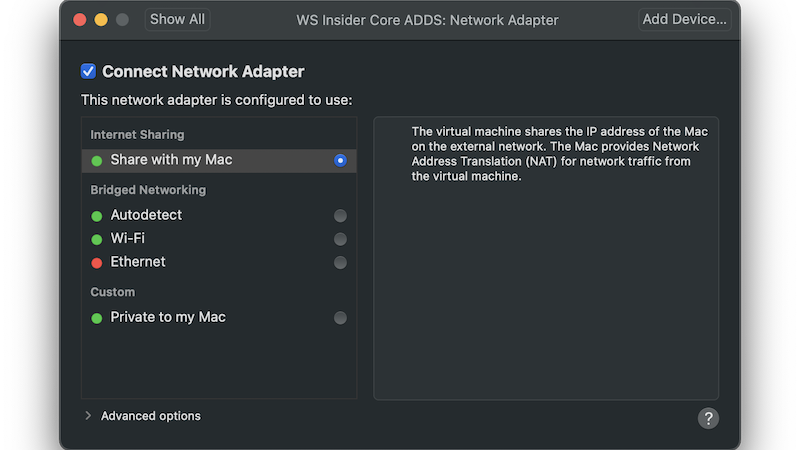
For my initial lab setup, I plan on deploying the Insider editions of Windows Server Core, Windows 10 Pro, and then building an Active Directory domain to manage the environment. Then, I added a virtualized macOS 11 Big Sur VM. In the future, I plan to deploy an IIS web server on my domain controller and the developer edition of SQL Server on another AD member Core server. I will be using Microsoft’s RD Client for macOS to connect to the Windows machines. To network the virtual machines together, I will use the “Share with my Mac” VMware Fusion networking option. From my home network perspective, there will only be one DHCP1 IP network address being used (by my iMac) and each VM will get it’s own private IP address thanks to the magic of NAT2.
For my next article in this series, I will discuss the setup process for Windows Server Core.
